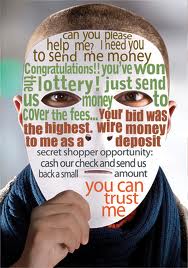
WARNING – 419 SCAM – AMERICA ONLINE PHISHING SCAM
Click here for previous posts sent by scammer Grey Watson.
From: hnfdhfghfh@yahoo.com
To: hnfdhfghfh@yahoo.com
Subject: From The Desk Of: Dr. Grey Watson194.72.251.4
Date: Mon, 11 Feb 2013 03:33:16 +0200
From The Desk Of: Dr.Grey Watson
Bank of America
Branch Offices New York
1680 Broadway, New York,
NY 10019, USA..
Vice Chairman on Investment Banking
Director, Credit Control Dept.
Email: drgreywatson@superposta.com
Attn: The Beneficiary,
TELEGRAPHIC TRANSFER NOTICE.
We are hereby officially notify you concerning your fund telegraphic Transfer through our bank, Bank of America, New York, to your bank account, which has been officially approved by the management of World Bank Swiss (WEBS) to credit the sum of US$10.5 Million into your bank
account.
Note that I have started processing your payment and every thing concerning the immediate remittance of your funds will be carried out within the shortest possible time from the time we received your? Below needed information.
Also be informed that the Governor of Bank in London (BL) will sign on your payment advice and a copy of the advice will be sent to the World Bank in Swiss for some record purposes. Meanwhile your information and your full contact details were received from our research manager, Barr.Paul Peterson on your behalf to FR for immediate release of your fund.
This fund was part of the lodged Late President Saddam Hussein of Iraq discovery fund with World Bank of Switzerland, which the Swiss Bank has decided to distribute it generously to help few lucky individuals and the American Government is in agreement with the Swiss Bank to distribute the fund to 700 hundred thousand people in America, Europe & Asia in other to help improve their businesses.
Therefore, reconfirm the aforesaid information accurately, because this office cannot afford to be held liable for any wrong transfer of funds or liable of any fund credited into an unknown account.
These are the information we needed to be reconfirmed by you.
1.Your Full Bank Account Details
2.Your Direct Cell or office phone to reach you
3.Your address of locations
4.Your full name
Finally, you are required to reconfirm directly to me the above information to enable me use it to process your bill of payment. Your quick response shall be mostly appreciated; all your response should be directed through our alternative email address for the immediate attention of the credit control department.
Yours Faithfully,
Dr. Grey Watson
Vice Chairman, Director, Credit /Telex Department.
EMAIL: drgreywatson@superposta.com
From: cindy l crossen crossen8@yahoo.com
Decatur-Avondale Estates Patch <noreply@patch.com>
Sent: Saturday, February 23, 2013 7:21 PM
Subject: From The Desk of:Mr. Fares D. Noujaim. Bank of America Branch Offices New York 1680 Broadway, New York, NY 10019, USA. Vice Chairman on Investment Banking Director, Credit Control Dept. Attn: The Beneficiary, TELEGRAPHIC TRANSFER NOTICE. We are hereby officially notify you concerning your fund telegraphic Transfer through our bank, Bank of America, New York, to your bank account, which has been officially approved by the management of World Bank Swiss (WBS) to credit the sum of US$18.5 Million into your bank account. Note that I have started processing your payment and every thing concerning the immediate remittance of your funds will be carried out within the shortest possible time from the time we received your, Below needed information. Also be informed that the Governor of Bank in London (BL) will sign on your payment advice and a copy of the advice will be sent to the World Bank in Swiss for some record purposes. Meanwhile your information and your full contact details were received from our research manager, Barr. Paul Peterson on your behalf to FRB for immediate release of your fund. This fund was part of the lodged Late President Saddam Hussein of Iraq discovery fund with World Bank of Switzerland, which the Swiss Bank has decided to distribute it generously to help few lucky individuals and the American Government is in agreement with the Swiss Bank to distribute the fund to 700 hundred thousand people in America, Europe & Asia in other to help improve their businesses. Therefore, reconfirm the aforesaid information accurately, because this office cannot afford to be held liable for any wrong transfer of funds or liable of any fund credited into an unknown account. These are the information we needed to be reconfirmed by you. 1.Your Full Bank Account Details 2.Your Direct Cell or office phone to reach you 3.Your address of locations 4.Your full name Finally, you are required to reconfirm directly to me the above information to enable me use it to process your bill of payment. Your quick response shall be mostly appreciated, all your response should be directed through our alternative email address for the immediate attention of the credit control department. Yours Faithfully, Mr. Fares D. Noujaim Vice Chairman, Director, Credit /Telex Department. Signed,Bank of America,New York sent you a link from Decatur-Avondale Estates Patch – International Community School hosts tours of their new site at the former Medlock Elementary School
From The Desk of:Mr. Fares D. Noujaim. Bank of America Branch Offices New York 1680 Broadway, New York, NY 10019, USA. Vice Chairman on Investment Banking Director, Credit Control Dept. Attn: The Beneficiary, TELEGRAPHIC TRANSFER NOTICE. We are hereby officially notify you concerning your fund telegraphic Transfer through our bank, Bank of America, New York, to your bank account, which has been officially approved by the management of World Bank Swiss (WBS) to credit the sum of US$18.5 Million into your bank account. Note that I have started processing your payment and every thing concerning the immediate remittance of your funds will be carried out within the shortest possible time from the time we received your, Below needed information. Also be informed that the Governor of Bank in London (BL) will sign on your payment advice and a copy of the advice will be sent to the World Bank in Swiss for some record purposes. Meanwhile your information and your full contact details were received from our research manager, Barr. Paul Peterson on your behalf to FRB for immediate release of your fund. This fund was part of the lodged Late President Saddam Hussein of Iraq discovery fund with World Bank of Switzerland, which the Swiss Bank has decided to distribute it generously to help few lucky individuals and the American Government is in agreement with the Swiss Bank to distribute the fund to 700 hundred thousand people in America, Europe & Asia in other to help improve their businesses. Therefore, reconfirm the aforesaid information accurately, because this office cannot afford to be held liable for any wrong transfer of funds or liable of any fund credited into an unknown account. These are the information we needed to be reconfirmed by you. 1.Your Full Bank Account Details 2.Your Direct Cell or office phone to reach you 3.Your address of locations 4.Your full name Finally, you are required to reconfirm directly to me the above information to enable me use it to process your bill of payment. Your quick response shall be mostly appreciated, all your response should be directed through our alternative email address for the immediate attention of the credit control department. Yours Faithfully, Mr. Fares D. Noujaim Vice Chairman, Director, Credit /Telex Department. Signed,Bank of America,New York ( bankofamericanewyork74@yahoo.com ) has shared the following event from Decatur-Avondale Estates Patch:
International Community School hosts tours of their new site at the former Medlock Elementary School
Return-Path: <crossen8@yahoo.com>
Received: from nm16-vm1.bullet.mail.bf1.yahoo.com (nm16-vm1.bullet.mail.bf1.yahoo.com [98.139.213.131])
by mtain-mh11.r1000.mx.aol.com (Internet Inbound) with SMTP id A2C3738000093
for <scammer419@aol.com>; Sun, 24 Feb 2013 12:30:10 -0500 (EST)
Received: from [98.139.215.141] by nm16.bullet.mail.bf1.yahoo.com with NNFMP; 24 Feb 2013 17:30:10 -0000
Received: from [98.139.212.200] by tm12.bullet.mail.bf1.yahoo.com with NNFMP; 24 Feb 2013 17:30:10 -0000
Received: from [127.0.0.1] by omp1009.mail.bf1.yahoo.com with NNFMP; 24 Feb 2013 17:30:10 -0000
X-Yahoo-Newman-Property: ymail-5
X-Yahoo-Newman-Id: 522462.61826.bm@omp1009.mail.bf1.yahoo.com
Received: (qmail 55302 invoked by uid 60001); 24 Feb 2013 17:30:10 -0000
DKIM-Signature: v=1; a=rsa-sha256; c=relaxed/relaxed; d=yahoo.com; s=s1024; t=1361727010; bh=0sc4nr+pqOlvq8SQpXImmwdM6buO4neJ6A98CgnR7X4=; h=X-YMail-OSG:Received:X-Rocket-MIMEInfo:X-Mailer:References:Message-ID:Date:From:Reply-To:Subject:To:In-Reply-To:MIME-Version:Content-Type; b=l7oknc4Vexm6cnniutjA9BE07XaVTBbvNGes6m3ENwmJfOUwbyDeiD9u7Sie3qONCX4wSVxq2I/f7hSr9rr9UTNDfixerWt7myBpzuOSkJGbvXpOXOTn29BESVGNDXiXmUNkDqnVj5SaSAuuMJOIT0cqYGDJRZuf0wcs2VTqauo=
DomainKey-Signature:a=rsa-sha1; q=dns; c=nofws;
s=s1024; d=yahoo.com;
h=X-YMail-OSG:Received:X-Rocket-MIMEInfo:X-Mailer:References:Message-ID:Date:From:Reply-To:Subject:To:In-Reply-To:MIME-Version:Content-Type;
b=rnjA+39ZkaGJwdGenoEM+KyV+QBnNj337v0bKIdY1acncE4VbDM6LWduWGPVQIjNekxRMVCel/TXXDPdiuM4Tozm0H+qi5hshzt9+kcTnGotMPITJqL3S+tJOWlj+YZg9wE+2esKrbH5jGrdNPH47Y70Pre7NCyMiewgRprjsRg=;
X-YMail-OSG: GJU8ve8VM1lpFYGT3isErhgajAAtLPGL9EhJeaK_ojXzb8v
9JV42Zv5sk7EYHgQa.aQGdcA1kSPrZ5zbFsNB2bwcqzCvkf_sgS64gxNh88s
lTt.a08JpkQ5FsHO25_JF37__JXIvMS66s5PcorkB4IP74WCRsP9bAU1Adu8
Zo097KmAYzSFfO_ze1CpK2nnQ3e5xwTgzL8FWoL3kiZB4lKmC5TE3qgCCdjl
sUVZJPvzqShwIweAGO9y.nttu9nq1n7JaWgkrUhH9D_5.ssVFq6pLq13feid
Yrx4VbJkE.HYUu4y5G1Xv1Q2exx_5Y4Ab4GxC9CC0SXPpkqsBDDpIhj5fW9k
yb8EzAtxnE6SuxUjBtWCSJgBHgauJXvgBGYW3Ot3pxDAw6ru6B5N.rTLCJmN
TqRuC8u8gWx5fj0quGWpsfVFSznraRMPwNIiWKIcqEantiCWZRkYkfEyfoy.
GOIKA9j9OZD0pjYP4tIzGaOf7WSyuJHprSwTR1DtULqVPZ8ZO9fqKSL_3IgU
Poib0rZDIufjYQrEdAQuDrHjYrHlqc0SjXDbZw0FN.RKH4hXk8VGPxLtJ0KH
RTGAnAWuWAjHFzri9gM5qli9HSZRkiG0i_psGmBDrL_LUakovl0QqfFKl.xa
EUXxaDNFprLwFqQxScrcmzc.H_xllhsVRQ.nKki.8xezTlm.doKfFcYOayyx
y9pj28M1n3vzqYM2mx80JmNRj.6vMmfzmcU2xHKZZdSah8Y0OCG_gUF5_fkP
.dsqjKWw5bChsZepZxAaGVWSN.n2pxxGU_9igzU7y5hr4VqG0DepqyJNXzQw
4cgb.a94zL2YvN1V_cIdl_RvGnTPETOv4IxZR0GIlU.Od7YrVCKhRqmWdFDm
bWMcjh.ebymekpwvD.JOTeRqlOIJ8TB5qE.DpHrlIR5IUtoBcKtRxFkjf71R
ZU43p58zhe.cRzdRDH7bCUktwHi0CuKsJrfdU3rmAm9vZdu3DhxOqvzRKJDR
TT_m1sVLErg–
Received: from [99.103.147.2] by web140801.mail.bf1.yahoo.com via HTTP; Sun, 24 Feb 2013 09:30:10 PST
X-Rocket-MIMEInfo: 001.001,CgoKY2luZHkgbCBjcm9zc2VuCgpGcm9tOiBEZWNhdHVyLUF2b25kYWxlIEVzdGF0ZXMgUGF0Y2ggPG5vcmVwbHlAcGF0Y2guY29tPgpUbzogClNlbnQ6IFNhdHVyZGF5LCBGZWJydWFyeSAyMywgMjAxMyA3OjIxIFBNClN1YmplY3Q6IEZyb20gVGhlIERlc2sgb2Y6TXIuIEZhcmVzIEQuIE5vdWphaW0uIEJhbmsgb2YgQW1lcmljYSBCcmFuY2ggT2ZmaWNlcyBOZXcgWW9yayAxNjgwIEJyb2Fkd2F5LCBOZXcgWW9yaywgTlkgMTAwMTksIFVTQS4gVmljZSBDaGFpcm1hbiBvbiBJbnZlc3RtZW50IEJhbmtpbmcgRGkBMAEBAQE-
X-Mailer: YahooMailWebService/0.8.134.513
References: <51296b17cce0e_2ac2333fce018d@patchfe-d26.ihost.aol.com.tmail>
Message-ID: <1361727010.45138.YahooMailNeo@web140801.mail.bf1.yahoo.com>
From: Cindy Crossen <crossen8@yahoo.com>
Reply-To: Cindy Crossen <crossen8@yahoo.com>
Subject: Re: From The Desk of:Mr. Fares D. Noujaim.
X-AOL-SCOLL-AUTHENTICATION: mtain-mh11.r1000.mx.aol.com ; domain : yahoo.com DKIM : pass
X-AOL-REROUTE: YES
x-aol-sid: 3039ac1d60df512a4e224459
X-AOL-IP: 98.139.213.131
Below are some other names, email and IP addresses used by the above Grey Watson –
BANK OF AMERICA NY USA secretary.accounts@morison.co.ke REPLY-ADDRESS: <bankofamericannyusa@yahoo.cn> (LMAO, CN? ISN’T THAT A CANADIAN ADDRESS? ALSO YAHOO IS A FREE EMAIL SERVER AND BANK OF AMERICA (NOT ‘AMERICAN’) WOULD HAVE AN ACTUAL DOMAIN)
RETURN-PATH: secretary.accounts@morison.co.ke
X-YAHOO-FILTER-BULK: 62.8.88.13
Subject: From The Desk of: Mr. Fares D Noujaim
41.206.84.120
FROM: ”Bank of America” <red4x4tj@yahoo.com> red4x4tj@yahoo.com
newyorkbankofamerica@yahoo.com
RECEIVED-IP: 62.8.88.2 by zmbs01.wananchi.com
Other scam addresses who’ve sent mail using the same receiving IP information
62.8.65.11
41.212.2.11
41.212.18.30
41.212.32.10
62.8.88.13